A Distributed Denial of Service (DDoS) attack is a malicious attempt to disrupt the normal functioning of a network, service, or website by overwhelming it with a flood of internet traffic. The goal of a DDoS attack is to make the targeted system or network unavailable to its users by overloading it with a large volume of requests, rendering it incapable of handling legitimate traffic.

Table of Contents
How does a DDoS attack work?
The basic functionality of a DDoS attack involves coordinating multiple devices, often compromised computers or servers, to generate a massive amount of traffic that is directed at the target. This flood of traffic can consume the target’s bandwidth, processing power, or other resources, making it difficult or impossible for legitimate users to access the targeted service.
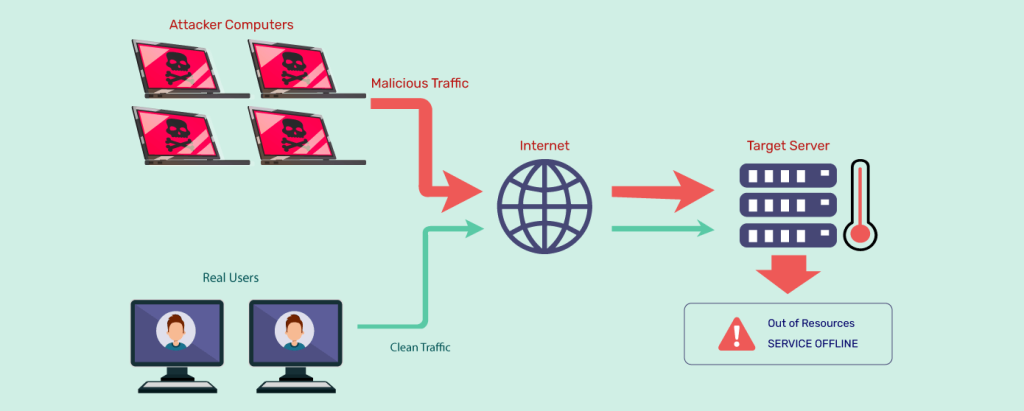
Recruitment of Botnets: The attackers first assemble a network of compromised computers and devices, known as a botnet. These devices are often infected with malware, allowing the attackers to control them remotely. The owners of these devices are usually unaware that their systems are part of a botnet.
Command and Control (C&C) Servers: The attackers operate from command and control servers, which are responsible for issuing instructions to the compromised devices within the botnet. These instructions include the target IP address, the type of attack to be launched, and other parameters.
Traffic Generation: The compromised devices in the botnet are instructed to send a massive amount of traffic to the target. This traffic can take various forms, including:
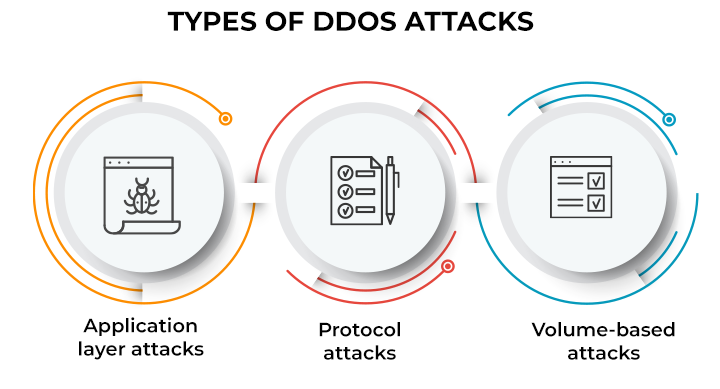
Types of DDoS attacks:
- Volume-Based Attacks: These aim to overwhelm the target with a flood of traffic, such as through UDP reflection/amplification attacks.
- Protocol-Based Attacks: These exploit weaknesses in network protocols to consume server resources and disrupt services.
- Application Layer Attacks: These target specific applications or services, aiming to exhaust server resources or exploit vulnerabilities in the application.
- Hybrid Attacks: These combine different techniques to create a more sophisticated and potent attack.
How to identify a DDoS attack
Identifying a Distributed Denial of Service (DDoS) attack involves vigilantly monitoring network and system behavior for signs of abnormal patterns or excessive traffic. An abrupt surge in network traffic, exceeding typical levels, is a common indicator of a potential Distributed Denial of Service attack. This may manifest as a significant increase in data transfer rates or a spike in connection requests.
Furthermore, degradation in network performance, such as slow response times or intermittent connectivity problems, can signal an ongoing attack. Service outages, particularly if users are unable to access websites or applications, may also point to a Distributed Denial of Service attack incident. Examining server logs for unusual patterns, error messages indicating failed requests or resource exhaustion, and analyzing the characteristics of incoming traffic, including source and type, can provide additional insights.

How to Protect Yourself from DDoS Attacks?
Protecting yourself from Distributed Denial of Service attacks involves implementing a combination of proactive measures and reactive strategies. Here are several steps you can take to enhance your defense against Distributed Denial of Service attack:

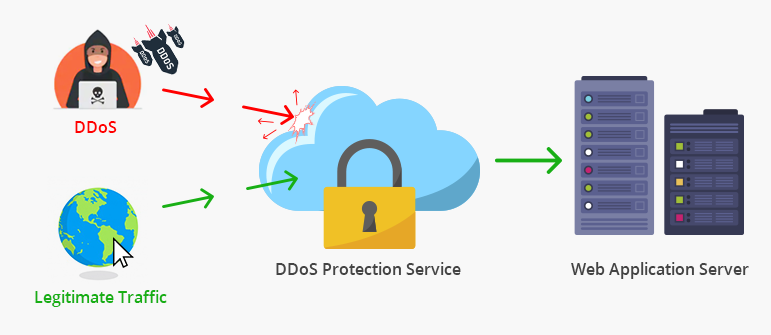
Implement DDoS Mitigation Services:
Consider using DDoS mitigation services provided by specialized cybersecurity firms. These services can help detect and filter out malicious traffic, ensuring that legitimate traffic reaches your network or service.
Network Redundancy:
Set up network redundancy and load balancing to distribute incoming traffic across multiple servers or data centers. This can help mitigate the impact of a Distributed Denial of Service attackk by spreading the load.
Cloud-Based DDoS Protection:
Utilize cloud-based DDoS protection services offered by major cloud service providers. These services can absorb and filter out malicious traffic, preventing it from reaching your infrastructure.
Content Delivery Networks (CDNs):
Deploy a Content Delivery Network (CDN) to cache and distribute content across multiple servers strategically located in different geographic regions. This helps reduce the impact of a Distributed Denial of Service attack by distributing the load and providing faster access to content.
Firewalls and Intrusion Prevention Systems:
Implement firewalls and intrusion prevention systems to filter out malicious traffic. Configure these systems to recognize and block traffic patterns associated with DDoS attacks.
Traffic Monitoring and Anomaly Detection:
Regularly monitor network traffic and employ anomaly detection systems to identify unusual patterns. Set up alerts to notify you of potential DDoS activity, enabling a rapid response.

Incident Response Plan:
Develop an incident response plan specifically for DDoS attacks. Define roles and responsibilities, establish communication channels, and have a step-by-step process for mitigating the impact of an attack.
Bandwidth Scaling:
Ensure that your network has sufficient bandwidth to handle traffic spikes. Scaling up bandwidth during periods of increased activity can help absorb the impact of a DDoS attack.
Rate Limiting and Traffic Shaping:
Implement rate limiting and traffic shaping measures to control the number of requests from a single source or within a specific time frame. This can help prevent the network from being overwhelmed.

Regular Security Audits and Updates:
Conduct regular security audits of your network infrastructure and keep software, firmware, and security solutions up to date. Patch vulnerabilities promptly to reduce the risk of exploitation.
Collaborate with ISPs:
Work closely with your Internet Service Provider (ISP) to implement traffic filtering and blocking at the network edge, reducing the impact of DDoS attacks before they reach your infrastructure.
It’s important to note that participating in or conducting a DDoS attack is illegal and unethical. Organizations use various methods, such as firewalls, intrusion detection/prevention systems, and content delivery networks, to mitigate the impact of DDoS attacks and protect their services. Additionally, law enforcement agencies worldwide actively pursue those responsible for launching such attacks.